A still from the film “π” (1998). Source: Artisan Entertainment
Here’s how the computer virus was born 34 years ago
COMPUTER VIRUSES have become the subject of a lot of worry in today’s technology world – outlets around the world report on news of various malware attacks compromising individuals in the millions, while experts scramble to keep up with the latest developments from hacker communities.
However, how did the “computer virus” as we know it come to be? The computer virus has origins as a conceptual idea from as far back as 1973 with the cult flick Westworld, where characters in a robot-staffed theme park discussed the spread of malfunctions in the androids, caused by some kind of infection-like virus.
Despite this bit of cinematic trivia, its actual roots begin with a student in California in the United States, Frederick Cohen, and his lecturer, Leonard Adleman, way back in 1983.
In celebration of their self-declared Antimalware Day, cybersecurity firm ESET marked the event with exclusive conversations with both Adleman and Cohen, to discover what really went on behind the scenes of their groundbreaking work, which today is the basis for much of our knowledge of computer threats.
According to the interview, Cohen — then a student at the University of Southern California’s engineering school — began experimenting with computer code that could exploit connected systems, jumping from affected and unaffected ones much in the same way a flu virus might infect a group of people.
A VAX 11/750 processor which Cohen used to write his computer virus. Source: Hampage
“I was in Len Adleman’s information security class at USC when the proverbial light bulb turned on,” Cohen said to ESET in an exclusive interview.
“I immediately knew that a virus could penetrate, and be used to exploit any connected general-purpose system. The only question was how quickly.”
After laboring for eight hours on a VAX 11/750 system — processing unit running the developer’s platform Unix — Cohen created the very first computer virus which was capable of spreading to all system users and gain control over its data and privileges. Across various experiments, the code was found to work within five and 30 minutes.
According to a statement from ESET, Cohen’s virus proved that a computer virus that could “infect” other programs, and embed a version of itself within it. The virus Cohen created was able to install itself, and quickly infect many systems.
Those initial experiments represent the beginnings of the age of malware, and serves as the basis for today’s reality, full of superbugs that are able to expand their research in our increasingly connected world. Cohen’s first attempt soon became a long experiment to test how quickly these computer programs could replicate. Cohen would go on to produce a groundbreaking paper called “Computer Viruses – Theory and Experiments” which would help define self-replicating programs as “viruses”.
Cohen explained to ESET that he took his program to Adleman, then his teacher, who would later go on to name the program a “computer virus” in reference to its “infectious” operations. Adleman was a well-known computer scientist then, having helped create the RSA (Rivest-Shamir-Adleman) encryption algorithm, and DNA computing.
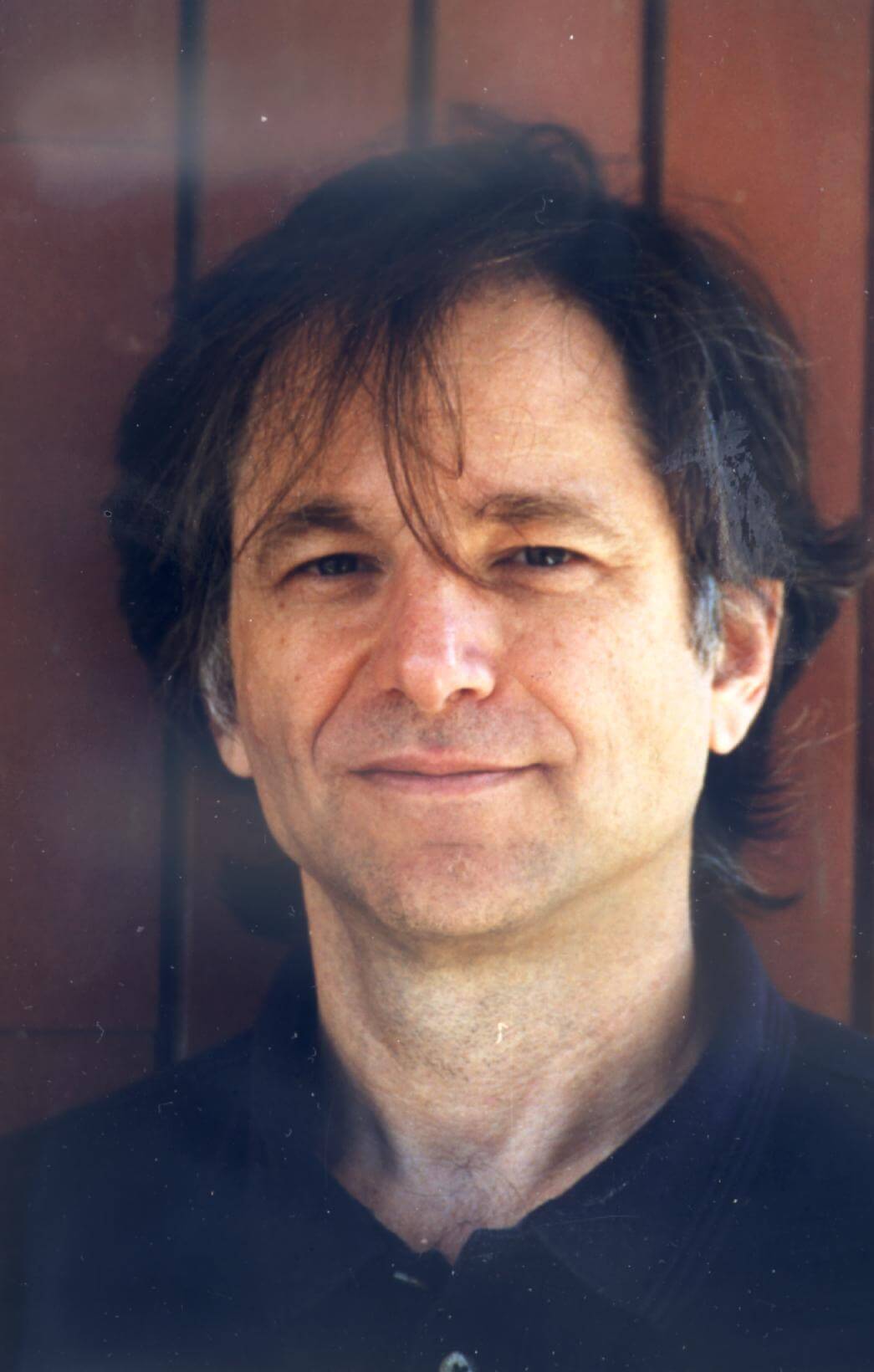
Leonard Adleman. Source: WikiCommons
“I recall Fred, who was a student at my class, coming up to me after class and saying ‘I have this idea for a new kind of computer threat’,” he recalled in an interview with ESET.
“He said, ‘I will write this program and make it available to all the users on our systems. I will advertise the program as doing something useful, like organizing the user’s files’.
“But when they uploaded the program, what it would actually do is surrender all control of their data and privileges to Fred.”
After discussing the project with Cohen, Adleman helped him acquire permits that would allow him to conduct his research on the university department computer systems. The project proved to be successful and gave the two men a glimpse into the future technological landscape.
“The program had done exactly what he had claimed it would do. It very rapidly was taken up by users of the system and all rights and privileges and data of the system were surrendered to Fred”, he recalled
Cohen continued experimenting with his viruses, always wresting control over computer systems, in an age without smartphones and personal computers. Adleman would later go on to supervise Cohen’s PhD.
Of course, as with all that success came the realization that these computer programs could be dangerous if put in the wrong hands. Cohen, “intensely interested” according to an ESET statement, continued to tinker with such code, but the university later revoked access when speculation about the potential harm of the computer virus became rampant.
“As a result of information technology, we live longer, better, easier, happier, etc. lives than ever before. And things on the whole seem to be getting better,” said Cohen.
“So far, the rewards seem to be worth the risks. But if we don’t learn to deal with the cyberwarfare issues, we may not continue to find it that way.”
He explained that the “fail and fix” approach to cybersecurity that is the current norm is not enough when it comes to defending our systems against attack. The lag in addressing potential risks, or the lack of investment in appropriate prevention programs is a huge contributor to our systems vulnerability, but is also an easily fixed situation.
“We wait for pain and then spend resources to alleviate it. The strength of fail and fix is that if nothing noticeable fails, you don’t spend any resources fixing,” said Cohen.
“The weakness is that lots of things fail, it may take you a long time to detect the failures (if you ever do), and the cost of fix far exceeds the cost of proactive efforts.”
“What we can do is the best we can do, our best try. And that’s what antiviral companies are doing,” said Adleman.
“You might just as well ask what do we do about infectious diseases that attack our bodies, and we do the best we can: we make vaccines, antibiotics, antiviral medications — But these are evolving things out there, so we have to keep doing our best”.
READ MORE
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
- Insurance everywhere all at once: the digital transformation of the APAC insurance industry
- Google parent Alphabet eyes HubSpot: A potential acquisition shaping the future of CRM