
Why IT gets excluded from digital transformation projects
EVERY SENSIBLE organization has plans for the future. Some plans are nascent ideas in board members’ minds of where the company might be headed and how the enterprise should develop and change according to changing circumstances.
Good businesses also plan for the negative too: business continuity planning is a vital part of ensuring the organization’s future in the event of things taking a turn for the worse.
Common elements to a business continuity plan (BCP) might include how the company would cope in the event of a flood at one of its branch offices or the loss of an important executive to another company. There might be a drop in the value of a key investment the company has made or, maybe, the company may be rocked by claims of fraud which funded lavish lifestyles.
Typically in charge of a BCP is a Risk Manager (RM), a member of personnel whose job it is to think the worst, and ensure (through testing and modeling outcomes) that the enterprise will suffer minimal losses and continue to function as best it can in the event of an unfortunate twist of fate.
With today’s businesses being, in the main, utterly dependent on information technology, why are IT departments not involved in risk management and continuity planning as much as they should be?
According to Gartner, 60 percent of digital businesses (and which business is not digital today?) will suffer major service failures due to an inability to manage digital risk.
Ensuring that digital security is one of the central tenets of any decision or project is therefore absolutely key. But what is apparent is that cybersecurity experts are often either not consulted, or consulted too late in a project’s lifecycle to be effective.

A survey conducted in 2016 reveals some alarming figures. A massive 76 percent of organizations agreed that cybersecurity considerations were added too late even in digital transformation (!) projects. If the IT department, where cybersecurity expertise resides, is excluded from digital project planning, what is going on?
Ingrained in our collective nature as human beings is creativity – after all, this is how the human race survived: by coming up with new ideas, adapting and evolving more quickly than other species. The creative mindset pervades the workplace.
Ideas are, given good staffing and management methods, fed into policy and decisions and eventually implemented for the good of the enterprise.
But so long seen as mere engineers, IT staff have a reputation for obstinacy and creating difficulty. In stereotypical terms, the “high-fliers” of the enterprise come up with “blue sky thinking”, which, when passed to the engineers of the traditional IT department, atrophies, and stalls.
It’s no wonder that projects reliant on tech are so often developed “under the radar”.
There are two main reasons for these attitudes across the enterprise, and these need to be understood if we are to address the issue of needing to get cybersecurity embedded into projects right from the very start.

Firstly, implementing even the most detailed of digital transformation plans requires a level of engineering minutiae that only a specialist IT department or contractor could be aware of. When the engineers work through the fine detail of implementation, previously unforeseen issues are often unearthed that can have major consequences on a project, and can be a source of delay.
Secondly, when the IT engineers are excluded from the creative process, the tendency is for IT to work “blind”, without a concept of the desired outcomes. By being excluded from the planning process, staff are not aware of the intention of the project from, for instance, a customer’s point of view, or from a business-oriented strategic standpoint.
Involving the enterprise’s engineers therefore right from the outset has two beneficial effects. Firstly, delays are minimized as intended outcomes are clear. And secondly, essential issues which keep RMs up at night (like cybersecurity concerns) can be integral elements of the project which will go on to protect the entire enterprise.
Cyber resilience planning should, of course, be a central theme running through any risk management plan.
For instance: when the data infrastructure is breached maliciously, what processes and systems are in place (and rehearsed) for data recovery from compromised technical infrastructure? Are systems duplicated with instant failover?
Conversations about security need to start early and should be considered an essential part of providing real business value, not regarded as stumbling blocks or sources of delay. If essential data breach mitigation measures prove difficult and take valuable time to implement, why do we complain?
With the number of digitally connected devices we rely on increasing rapidly, threat intelligence, incident response planning, and cybersecurity risk assessment will significantly reduce any organization’s risk footprint. But getting measures in place needs to come early.
Here are three providers of cybersecurity services and solutions which we at Tech Wire think any business considering digital transformation should consult:
NTT SECURITY
As the specialized security company and center of excellence in security for the global conglomerate NTT Group, NTT Security focuses entirely on information security and risk management, aiming to protect organizations from the increasing threats posed by cybercrime and other issues of malicious data compromise.
The company bases its approach on securing digital business transformation via three pillars consisting of strategic consulting, technical consulting and the provision of managed security services.
NTT Security’s thought leadership is particularly relevant in its consideration of how IT departments need to get involved from the get-go for any digital transformation project. Organizations at different stages of cybersecurity maturity need to work with the right experts to navigate the options available to them in their digital transformation journey.
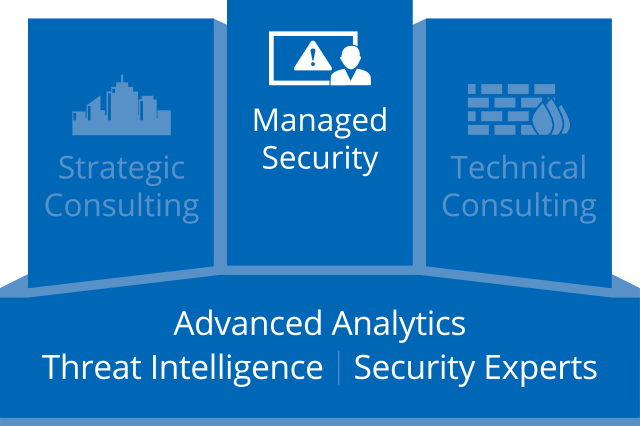
With visibility into 40% of the global internet traffic, NTT Security continuously gathers data from a wide number of sources, turning vast amounts of data into usable intelligence. Its Global Managed Security Service Platform (GMSSP) is a proprietary offering and uses the agglomeration of advanced analytics, machine-learning, and real-time threat detection and event correlation. Organizations are provided with current, emerging and applied threat intelligence along with actionable recommendations to address security incidents in line with their risk strategy. Threat research is leveraged on NTT’s global internet infrastructure, clouds, and data centers along with third party intelligence feeds, proactively monitoring and responding to exploits, malware and other techniques used by threat actors.
NTT Security’s offering protects organizations whose IT and data provision is in-house, in the cloud or across a hybrid model – or is transitioning to any combination of these topologies. Wherever an organization’s current place in the cybersecurity journey may be, NTT Security is keen to start cybersecurity considerations as early as possible.
NTT Security’s proactive approach and business-oriented methods provide a gold standard for data security in a technologically-focused world.
IBM
Big Blue’s behavioral analytics capabilities made the news a few weeks ago with a new initiative designed to help spot bogus bank accounts set up by criminals to handle monies from crime; so-called new account fraud (NAF).
But in the larger marketplace, IBM offers a full consultancy and security implementation service for organizations, as well as a managed security service for on-going protection.

The company’s penetration testers operate under the IBM X-Force Red banner, and that service’s portal aggregates all security testing activities, be they in-house, third-party or undertaken by IBM consultants.
While most security companies are keen to promote their use of machine learning, IBM’s Watson AI engine is of course, very well known even outside of tech circles.
IBM’s QRadar Advisor uses Watson to correlate unstructured data (human-created content, designed for humans to read – such as blogs and discussions on forums/chat channels) to add an extra string to the cybersecurity bow.
The company is aware that specific industries have, typically, different security requirements; each exhibits its own specific faultlines in data defense.
While compliance, for instance, affects all, certain data-intensive institutions (such as financial organizations) will need to be especially aware of the implications. IBM’s global reach allows it to be the go-to advisor at all levels and in all areas of the enterprise.
FIREEYE
The US-based company is currently spending some US$20 million relocating all its staff to its Milpitas, California headquarters, and while its 2017 Q4 earnings are expected to be less than predicted, the company has a well-proven track record in protecting enterprises from cyber attack.
As well as offering services in discreet markets, such as endpoint security, the company also offers a forensic service which can pinpoint the causes of security breaches.

FireEye also offers a meta-approach to IT security, which integrates and automates existing tech and security systems across an organization, and provides overarching security cover.
Internal IT staff can make use of FireEye’s ThreatSpace, a service which allows a company’s staff to assess and develop their own cybersecurity skills.
For those businesses which do not have an internal IT security facility (or wish to outsource the service), FireEye also advertises a security-as-a-service product, which provides experienced cybersecurity staff and FireEye’s not insignificant intelligence gathering capabilities, in order to protect the enterprise.
With the financial returns on cybercrime becoming increasingly lucrative, the company employs staff whose training and background is in precisely the same areas as the majority of “black hat” figures. To effectively combat digital crime, FireEye knows that staying up-to-date with the latest attack vectors and methods is essential to remediate risk.
READ MORE
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
- Insurance everywhere all at once: the digital transformation of the APAC insurance industry
- Google parent Alphabet eyes HubSpot: A potential acquisition shaping the future of CRM
