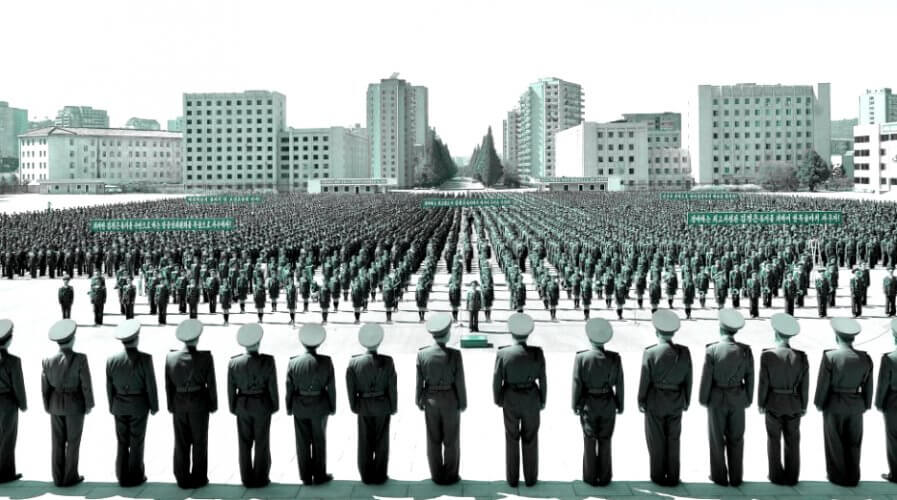
Members of the People’s Security Council take part an anti-U.S. rally, in this September 23, 2017 photo released by North Korea’s Korean Central News Agency (KCNA) in Pyongyang. Source: KCNA via Reuters
North Korea and US scale up for wider cyber war
THE CYBERSECURITY war between North Korea and the rest of the world appears to be taking a turn for the worse.
A private security company, FireEye has identified a North Korean cyber infiltration group called APT37 which has raised its sites from its previous concentration on purely South Korean targets to a more scattergun approach to cyber espionage.
At the same time, US authorities have formulated potential plans for a series of what it terms “bloody nose” attacks on targets in North Korea, which will focus on digital warfare rather than a conventional attack, according to UK news organization, The Daily Telegraph.
The new targets for the APT37 group, as revealed by FireEye, include a Middle Eastern company which had previously worked with North Korean authorities in telecommunications but whose venture had ‘gone south’. Furthermore, individuals working for Olympic organizations, a journalist associated with human rights issues in North Korea, and a Japanese party concerned with UN missions on sanctions have also been affected.
While the number & type of targets for the North Korean attacks have changed and broadened, the methods employed by the group remain much the same. Focusing primarily on phishing attacks in the first instance, the group sends Microsoft Office documents to its targets which, once open, drop malicious payloads into machines’ systems.
The variants of malware deployed in this way collect system information, take screenshots and remotely download further code from sites controlled by the group.
The hacking group seems quite quick to adopt newly publicised vulnerabilities, developing their specific tactics after only a few weeks from when vulnerabilities are publicised. FireEye’s report states this aspect “suggest[s] a high operational tempo and specialized expertise.”
According to sources for The Telegraph, for the last few months, the US has been laying the groundwork for cyber attacks against North Korea which will be routed through South Korea and Japan, where the US has a significant military presence. Preparations include installation of network infrastructure such as fibre cables, and the setting up of virtual listening posts from where government agents will attempt to access the North Korean Internet.
American analysts with experience in other areas such as the war on drugs are being reassigned to the new Korea Mission Centre, which is being run by the CIA.
In addition to our core behavioral/sandbox detection of #APT37 (Reaper), @FireEye develops resilient named detections for custom malware.
This provides customer context and telemetry.
It's probably a good time to make sure you aren't seeing these alerts: https://t.co/73LwHWfTXo pic.twitter.com/4jmcSbfwdO
— Nick Carr (@ItsReallyNick) February 20, 2018
The cyber war between North Korea and the rest of the world has heated up recently, with reports of the rogue state being behind the theft of ¥58 billion from Japanese cryptocurrency exchange Coincheck at the beginning of this year.
North Korea is thought to have mobilized around 6000 individuals to wage a virtual war against its enemies, and the choice of battleground may well suit an American administration particularly sensitive to physical casualties among US personnel in conventional conflicts, with the associated imagery of body bags being flown home.
As well as previous attacks laid at the door of the North Koreans such as the WannaCry incidents, a further malware instance termed “DogCall” and a wiper tool “RUHappy” have also been deployed.
“An individual we believe to be the developer behind several APT37 malware payloads inadvertently disclosed personal data showing that the actor was operating from an IP address and access point associated with North Korea,” said FireEye.
READ MORE
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
- Insurance everywhere all at once: the digital transformation of the APAC insurance industry
- Google parent Alphabet eyes HubSpot: A potential acquisition shaping the future of CRM




