
Taking no chances: risk and control monitoring for 2019 and beyond
The go-to tool for anyone in the risk assessment business is the spreadsheet. Its tabulated columns have always been ideal for a function in the enterprise which has had to enumerate its work so that the business can make carefully informed decisions.
The spreadsheet was, in fact, the application that ran on the first computers in the 1980s and changed the role of the emerging technology from a hobbyist’s plaything to a bona fide business tool. Apple’s first fortune, founded on the Apple II computer, was driven by the popularity of Visicalc, probably the first spreadsheet application in mainstream business use.
For an old technology (nearly 40 years is a long time in computing), spreadsheets are in use to a degree in modern enterprises today that those first software pioneers couldn’t have possibly imagined. Even in the least number-driven creative departments in the modern business, you’ll find spreadsheets – they’re naturally abundant.
In risk management, it may be time to bid farewell to the venerable spreadsheet, however. Not because the technology is failing as of itself, but rather the environment in which risk monitoring & control now need to take place has moved on, making the spreadsheet unsuitable for purpose.
The reasons that make spreadsheets unsuitable for risk management today are the same ones that are often called out as businesses look for CRM or ERP solutions to replace spreadsheets. Despite the protestations of the developers, spreadsheets are problematic because they are:
- Prone to human error
Typing into spreadsheets allows errors to creep in made by distracted (or bored) staff.
ACL
Additionally, as the capabilities of spreadsheets are stretched and extended by use of macros, the citizen coder’s efforts may be lacking.
- Candidates for file corruption
Single files are more prone to corruption than even the simplest of non-relational databases.
The larger and more complex a spreadsheet becomes, the more chance there is of its movements and sharing (see below) creating catastrophic file loss – resulting in time lost as backups are recovered and missing work replaced.
- Difficult to share
The exchange of spreadsheet files between individual users will always cause confusion as to which version is canonical. Sending sheets from A to B carries risks, in terms of possible corruption (see above) but also increases cybersecurity risk.
- Unsuitable for multiple users
Despite the best efforts of cloud-hosted versions of spreadsheet apps, the ability for several users to simultaneously edit a document is a slightly dubious add-on to this very old technology.
But it’s not just the nature of the spreadsheet that means that risk assessment managers are looking further afield for the next generation of software which helps and empowers. There is also a number of changes to the enterprise’s environment that mean conventional risk management solutions and systems need replacement.
Firstly, the sources of risk are now much more numerous. To go back to the 1980s again, we see there was no cybersecurity risk to speak of. Nor was there the quite the weight of regulation that enterprises now have to bear – a weight which varies from region to region, country to country.
Secondly, digitization itself has led to a dispersal of relevant information. Data that needs garnering for risk management purposes may now live in HR records, social media feeds of employees & employers, in a bank’s customer data, in IT log files, and even in the transaction records held by cloud services.
Thirdly, there is now an onus on institutions of all colors to proactively prove their compliance to new regulations and advisories. Gathering the information required is a complex and time-consuming undertaking without the right automated systems in place – and many of those systems are shared with risk management functions.
The increase in compliance-related spending has further tightened most enterprises’ purse strings, so risk managers need to find the best practices and systems which will allow them to make timely, informed decisions with fewer resources to help.

Here at Tech Wire Asia, we have considered two providers of digital, automated risk management platforms for businesses that take risk management seriously in the world that has become a great deal more complex in the last 30 years – but a world in which the last three or four years has seen an accelerated pressure on risk management.
When choosing a new system, or an update to legacy procedures, we would advise considering the following key indicators:
- Look for adaptable analytic models. Static metrics can be over-simplistic, and more useful indicators will be based on anomaly detection, a realization that baselines are moving, and the shifting relationships between multiple data points.
- Seek automation where appropriate. The capability to draw data from multiple data sources is important but is difficult to manage without automated routines which will pull or push data via APIs or other discreet interfaces between systems – finance, HR, cybersecurity, and so on.
- Use visualization and reporting. Part of the challenge for any function in the enterprise is buy-in, so visual tools will help present the risk manager’s case. Additionally, alerts of changing events or the emergence of new trouble-spots gain significant impact on even the most rudimentary dashboard (although the two suppliers listed below go well above and beyond that base level).
- Collaborate. Tools which allow all stakeholders to discuss and vote on KRIs means that no single individual needs to bear sole responsibility for risk assessment and management. Mobile-friendly tools in this area are particularly compelling.
- Integrate with other functions. Risk management platforms should be able to integrate with other systems; similarly, risk managers need to liaise with and work alongside the broader range of stakeholders affected by compliance, risk, and cybersecurity.
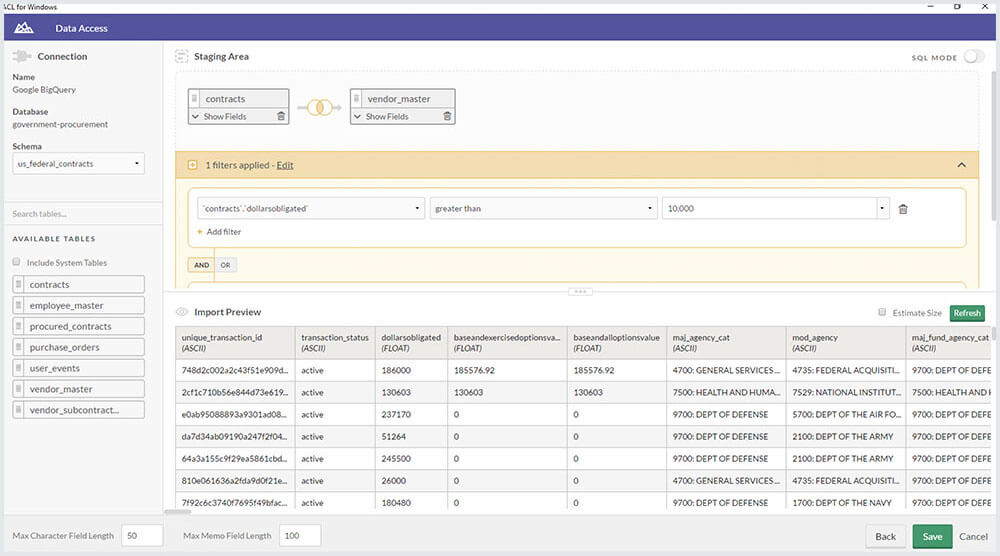
ACL
For more than 30 years, ACL has had an extensive portfolio of clients across various industries who seek transformative solutions in risk assessment, management, and audit. ACL is based in Vancouver, Canada, and has cemented its foothold with a significant presence in APAC region over the years.
From its vantage point, the company’s longstanding experience speaks volumes about its risk control & management solutions, which are designed to make sense of an organization’s priorities: different signals and procedures clamor for attention, once the enterprise starts to rely on different systems: ERP, CRM, HRM, ITsec, and so on.
It draws together mission critical systems that need to be monitored in real-time for effective risk and control, allowing companies who use ACL to meet internal quality management standards of the highest caliber, and also over-perform when it comes to regulatory compliance.
By connecting vast amounts of operational data, organizations also move away from the disadvantages of periodic risk management reporting (even weekly reports just don’t measure up – especially in IT security standards), with a real-time risk management platform that enables immediate action on any red flags.
Additionally, insightful reporting and a granular level of remediation automation create a market-leading risk control platform – modern, multi-user, integrated and future-proof.
IBM
Big Blue has two main channels via which its customers can better manage risk in their enterprise. Firstly, by combining IBM Algorithmics and OpenPages, companies can leverage the substantial power of both these platforms to help satisfy regulatory compliance, but also quantify risk right across the organization.
In addition to governance, IBM also offers specific areas of its platform which address banking book risk assessments, loss event tracking, insurance risk, and overall scenario analysis. The solution gathers a variety of risk indicators not limited to purely financial functions.
There’s also a cloud-based risk management solution for those companies which prefer to use the platform as a service, but in either deployment, the risk control solution uses a single data source which draws together information pertinent to risk from right across the enterprise.
Whether it’s part of a more full, far-reaching IBM deployment, or operating as a standalone risk control solution, IBM’s big data analysis and processing capabilities will encompass the multiple data sources required in today’s risk assessment and management function.
*Some of the companies featured on this editorial are commercial partners of Tech Wire Asia
READ MORE
- The criticality of endpoint management in cybersecurity and operations
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
- Insurance everywhere all at once: the digital transformation of the APAC insurance industry
