
How compliance and security became central to digital transformation thanks to Qualys
Hitting the twin targets of statutory compliance and low levels of cybersecurity vulnerability is a tall order. If either the compliance or security box is ticked, there’s no guarantee that the other element of staying safe is satisfied too.
Nor is there any surety that the situation will remain. The ever-changing legislative positions all around the world with regards to data regulation and the ingenuity of hackers and bad actors mean that the enterprise simply can’t stand still, on either score.
Maintaining a centralized, single source of truth, for all configuration items in scope is foundational. Therefore, it’s imperative to see a CMDB (configuration management database) that keeps its internal data repositories fully up to date — and by up-to-date, we mean, right up to a few minutes ago. Ceasing reliance on static data for IT audits is vitally important when organizations undertake their digital transformation journeys, as every new technology feature, app, or service designed to drive the company further along the digitization curve may have significant security or compliance ramifications.
But by “baking in” the two aspects of data regulation compliance and an active cyber security footing, companies of any size can progress, knowing that their efforts are, to the utmost extent, protected.
At the core of even the most advanced CMDB there has to be an up-to-the-moment, accurate snapshot of all IT assets. That means next-generation CMDBs are more than merely databases to tick compliance boxes. Gathering that information ‘live’ across a shifting, global hybrid topology is firmly the extperize area of Qualys, a company that’s expanded our concept of a compliance and vulnerability solution.
Its platform forms a central ingredient for new-gen CMDBs, and furthermore drives digital transformation of the entire enterprise. That’s because it provides a real-time and proactive framework of monitoring, oversight, and security right across the IT stack. It can help ensure adherence to internal policy, drive change in the minutiae of IT strategy, and keep the business’s overall strategic direction firmly on track.
The Qualys Cloud Platform uses very lightweight, configurable code snippets (Cloud Agents) that can be attenuated to be as busy or quiet (in terms of network activity) as required: the more crucial the system, the more capability you may wish to assign to the Cloud Agent.
Of course, the behavior and responses of each Cloud Agent are highly configurable without massive redeployments. Operators can drill down into a single resource and add or edit feature sets according to the instance’s role. Assets can be grouped and assigned tags for collective management of information. The Cloud Agent is available on all endpoint types, from AIX to Windows, and each report in real-time to the cloud-based Qualys engine.
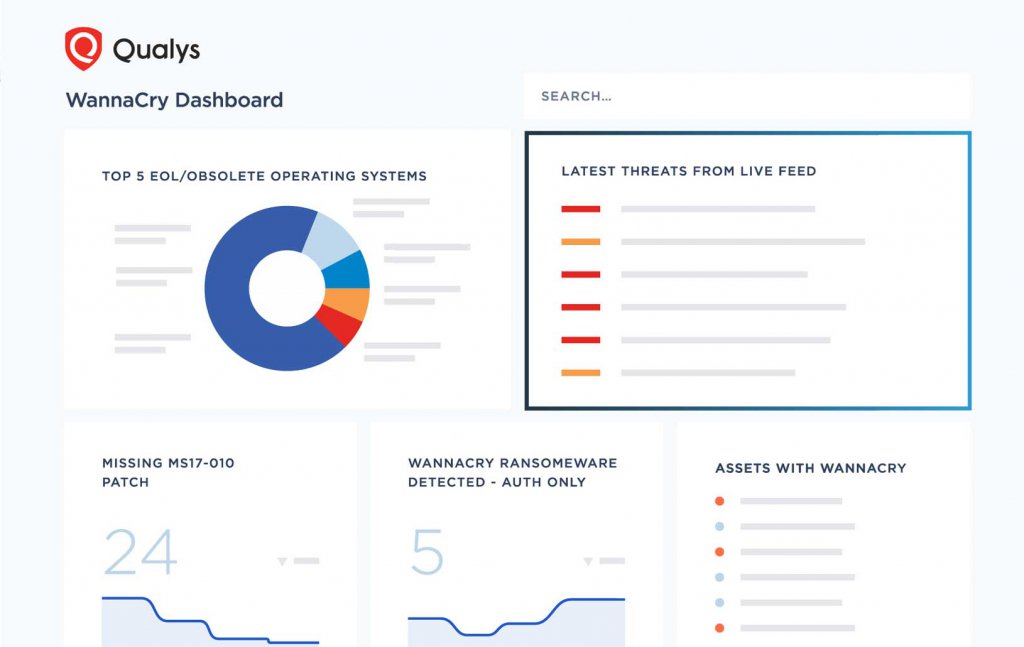
Source: Qualys
As a central plank in the digital transformation process, the Qualys Cloud Platform provides the type of information that’s (strictly) outside the immediate remit of compliance and security — if the information is there, one must question why the enterprise shouldn’t use it? Therefore, — to take a few examples — instances of unauthorized software can be spotted immediately, where they’re operating and to what systems the user has access.
Similarly, the Platform can identify software in danger of moving out of compliance, either with local legislation or falling foul of changing or expiring licenses. That same information type can help with wholesale updating and migration plans, in software, OS, and hardware: for a company serious about its digital transformation, that facility alone is worth the investment.
Learn more about how Qualys can drive value digitally right across the enterprise. Sign up for the free Global IT Asset Inventory and begin your digital transformation journey with compliance and security at the core.
READ MORE
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
- Insurance everywhere all at once: the digital transformation of the APAC insurance industry
- Google parent Alphabet eyes HubSpot: A potential acquisition shaping the future of CRM
