
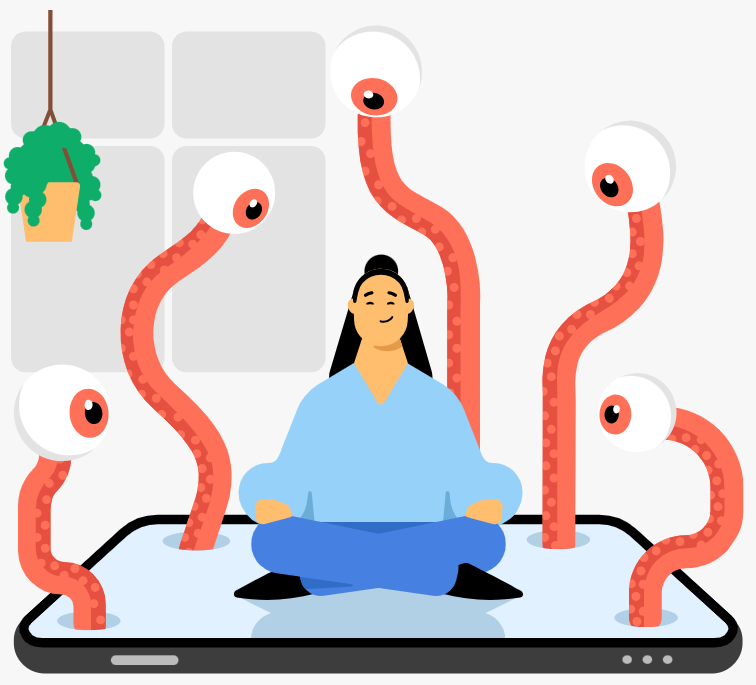
Navigating and managing cybersecurity risks while you relax. (Source – Shutterstock)
Managing the risks: How your digital relaxation habits affect your cybersecurity
- Survey links daily tech use for relaxation to higher cybersecurity risks.
- Streaming and social media collect data; lowered attention invites cyberattacks.
- Managing cybersecurity risks in your down-time is crucial, because your defences are lowered.
Cybersecurity specialists are growing increasingly uneasy about the widespread practice of utilizing electronic devices for relaxation purposes. This sense of unease has been fueled by a recent Cint survey sponsored by the renowned cybersecurity firm, NordVPN. The results were astonishing, with 96% of respondents indicating they use technology to decompress daily. While the numbers might seem innocuous or even beneficial at first glance, the trend has significant ramifications for cybersecurity.
Individuals frequently use electronic gadgets like tablets, smartphones, and smart TVs to unwind. Whether it’s binge-watching a gripping series on Netflix, HBO, or Disney, scrolling through aesthetically pleasing Twitter feeds, or simply meandering through various websites, they tend to enter into a mental state characterized by decreased alertness and increased vulnerability.
This “off-duty” mindset often results in lapses in basic cybersecurity precautions. Users may overlook even fundamental measures like scrutinizing URLs for authenticity, treating unexpected communications with skepticism, and being mindful of granting app permissions.
Managing cybersecurity risks in streaming services and social media platforms
Moreover, many are unaware that the content they access during these moments of relaxation is often data-hungry. Streaming services like Netflix, for instance, delve into your viewing history to generate personalized recommendations. Similarly, social media platforms like Instagram and Facebook meticulously track user activity and engagement metrics to curate custom-tailored content feeds.

Users are unaware of digital privacy during their relaxation time. (Source – Shutterstock)
While this data-driven customization enhances the user experience, it also means accumulating vast reservoirs of sensitive personal information. In a relaxed state of mind, users are significantly less likely to scrutinize or even be aware of these invasive data collection practices.
Consequently, this combination of relaxation and technology presents a paradoxical issue. The tools people turn to for peace may be actively eroding their situational awareness regarding potential cybersecurity threats. It’s an alarming scenario: a state of relaxation inadvertently becomes a playground for cybercriminals. These nefarious individuals rely on these moments of lowered attentiveness to initiate scams, deploy phishing emails, or even infect devices with malware.
Within these seemingly benign intervals of digital relaxation, people’s digital security could be most compromised, a reality that has cybersecurity experts increasingly sounding alarm bells.
Device usage patterns between televisions and smartphones
In more detailed terms, the survey also sheds light on the frequency of device usage for relaxation. 60% of respondents confessed to turning to their devices multiple times throughout the day for brief moments of relaxation. Moreover, 21% admitted to doing so at least once daily. The gadgets of choice for such activities were quite revealing.
Televisions generally retain their crown as the foremost device for hassle-free entertainment, securing 70% of respondent preference. However, smartphones are fast catching up, with a 69% usage rate. Remarkably, in countries like Italy, Malaysia, and Spain, smartphones have already eclipsed televisions as the go-to device for relaxation.
The survey provided significant insights regarding the types of activities people engage in while relaxing. A majority, around 66%, opted for watching television as their top relaxation activity, closely tailed by listening to music at 63%. However, there were interesting exceptions.
In countries like Spain and Switzerland, listening to music was slightly more popular than television. In Australia, streaming services outperformed traditional TV, and in Malaysia, the usual leader, television, ranked fourth after music, streaming, and aimless social media browsing.
Cyber threats lurking around to infect your devices. (Source – NordVPN)
Adrianus Warmenhoven, a leading cybersecurity analyst affiliated with NordVPN, underscored how the technological landscape of relaxation devices has evolved to include new risks. “In 2019, the FBI released a warning stating that smart TVs can make users vulnerable to surveillance and attacks by bad actors. Since then, user security technology has become more advanced, but internet-connected devices remain vulnerable,” he elaborated.
His concern also extended to smartphones, which have become the second most popular device for relaxation worldwide. “When people are relaxed, they often forget about possible cybersecurity risks. Smartphones are especially at risk because today, no other gadget knows more about its user. That makes smartphones a very appealing target for hackers,” Warmenhoven added.

Plans are afoot to make managing cybersecurity threats easier while people relax.
The survey found that two-thirds of respondents chose watching television to unwind, while another large proportion preferred listening to music. Over half of the survey participants also enjoyed streaming television shows or movies, or engaged in video watching on platforms like YouTube or TikTok.
Other popular activities included perusing social media feeds, with 45.7% of survey participants acknowledging this, and engaging in online conversations with family and friends, noted by more than a third of respondents as a form of relaxation.
Protecting your peace
For those concerned about managing cybersecurity risks while relaxing, Warmenhoven offered some advice:
- Keep your software updated: regular updates can shield your devices from known security risks.
- Equip your devices with cybersecurity tools: using an antivirus, a VPN, and a password manager can provide a robust defense against potential intruders.
- Exercise caution when downloading apps: always research and verify that a credible source develops the app.
- Avoid unofficial app stores: these marketplaces are often infested with malware-ridden applications.
- Use secure wi-fi connections: always be cautious when connecting to unfamiliar networks and use a VPN whenever possible.
- Always be alert: avoid clicking on dubious links, never share your personal information with strangers, and always question unsolicited communications.
Here are some more tips from NordVPN.
READ MORE
- Safer Automation: How Sophic and Firmus Succeeded in Malaysia with MDEC’s Support
- Privilege granted, not gained: Intelligent authorization for enhanced infrastructure productivity
- Low-Code produces the Proof-of-Possibilities
- New Wearables Enable Staff to Work Faster and Safer
- Experts weigh in on Oracle’s departure from adland






