
(Source – Shutterstock)
Understanding the cyber crime professional network
When it comes to cyber crime, how much of it is actually solve? What happens when an organization experiences a ransomware attack? Do they pay the ransom immediately or do they try and negotiate with the cybercriminal group to lower the ransom? How much of a role does law enforcement play when negotiating with cybercriminals? Can a cybersecurity vendor negotiate on behalf of an organization with the cybercriminal group?
These are just some of the questions an organization may have to know the answer to if they are ever victims of a ransomware attack. Unfortunately, for most businesses today, even with a backup, getting the data back from a ransomware attack is a prerogative simply because the information exposed is a huge risk.
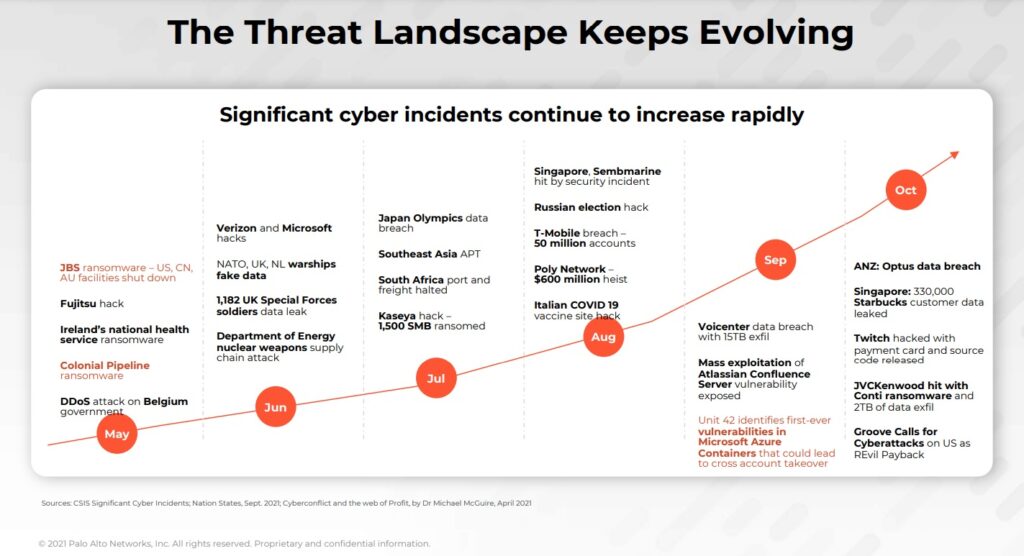
Over the last few months alone, the number of ransomware attacks across the world has increased tremendously, despite increased cybersecurity protection by most organizations. In Southeast Asia, the increasing number of attacks has witnessed businesses and even governments speeding up their adoption of cybersecurity and also looking at newer ways to secure their data.
In fact, according to Palo Alto Networks’ 2022 Incident Response report, business email compromise and ransomware make up 70% of the cases handled by their Unit 42 threat intelligence team. The report also highlighted that ransomware demands can be as high as US$30 million, with ransom payouts reaching about US$8 million on average.
Ransomware-as-a-service is helping drive the increase, especially among unskilled threat actors. At the same time, cyber attackers are also using multi-extortion techniques to maximize their profit.
Communicating with ransomware groups

Wendi Whitmore, Senior Vice President at Palo Alto Networks Unit 42
According to Wendi Whitmore, Senior Vice President at Palo Alto Networks Unit 42, the ransomware payout back was only US$10,000 when they first started the reports in 2016. The amount has increased exponentially and cybercriminals have increased their professionalism as well.
“They (Ransomware groups) run their organizations very much like a professional business. We will consistently negotiate and communicate with them. And you can see that the person on the back end is organized and pretty sophisticated. They genuinely oftentimes feel like the work that they are doing is legitimate security work, which has a very different payment model, one that is not nearly legal or certainly not ethical,” commented Whitmore.
Whitmore also pointed out that Unit 42 is working with providers that are familiar with ransomware groups and work closely with intelligence and law enforcement.
“There are organizations we work with if they’re interested in paying a ransom because they don’t have access to the data. We provide guidelines to work with law enforcement and make those introductions if they don’t already exist. If a ransomware group is unpredictable, like getting paid but they’re not providing the data back, we’re going to come up with intelligence and not provide a recommendation to pay the ransom,” added Whitmore.
At the same time, ransomware groups are pretty much predictable today. They want to make a profit at the end of the day from their cyber crime and also want to be known for it. As such, Whitmore said that some of these ransomware groups even have their own customer service and have surveys for organizations to fill out after a ransom is paid. They pride themselves on the good of returning the data in a very timely manner.
(Source – Palo Alto Networks)
The cyber crime ecosystem
While the process of communicating with ransomware groups can be complicated, paying the ransom is also another issue. Ransomware groups today insist on being paid in cryptocurrency with Bitcoin being the popular currency. The payment takes place in darknet markets, making it difficult to identify the perpetrators.
For Vicky Ray, Head of Unit 42 threat intelligence at the Asia Pacific and Japan, collaboration and information sharing with global law-enforcement agencies are critical in taking action against the perpetrators.
Ray also pointed out that contrary to popular belief that the dark web is where most cybercriminal activities take place, underground forums are now becoming an ecosystem where different types of cybercriminals collaborate. Ray explained that underground forums are becoming platforms whereby people share everything for the cybercrime industry.
Be it getting marketing capabilities to designing graphics for ransomware as a service, underground forums represent a proper business ecosystem.
“If you take a look at the many breaches in this region in the past couple of weeks, a lot of those leaks are not in the dark. It’s actually in these kinds of underground forums, where it is basically accessed by a lot of these cyber criminals. Not only do they sell tools and capabilities, but they are also selling PII-sensitive data which has been stored. So it is a big lucrative market out there. A lot of people are collaborating,” said Ray.
As such, Unit 42 provides the cyber crime intelligence to law enforcement bodies like Interpol in taking down such forums and also apprehending the cybercriminals. Palo Alto Networks is also part of the Cybersecurity Alliance, is a non-profit organization on a mission to create a more secure, interconnected world.
A proactive approach

Sean Duca, Vice President and Regional Chief Security Officer for JAPAC at Palo Alto Networks
With ransomware attacks expected to increase, more businesses are now moving towards a proactive approach in cybersecurity instead of just being reactive. In the past, companies would have some basic cybersecurity and would only react when a breach happens. However, given how complicated and costly ransomware attacks can be, the proactive approach to cybersecurity is becoming increasingly adopted.
Sean Duca, Vice President and Regional Chief Security Officer for JAPAC at Palo Alto Networks has been working actively with businesses in Southeast Asia to understand their problems and help them in their cybersecurity journey.
For context, 94% of organizations in Southeast Asia have experienced an increase in cyber attacks in 2021. Since then, 92% have made cybersecurity a top priority with 90% also looking to evolve their cybersecurity strategies. Two in three businesses are also planning to increase their cybersecurity budget, with 96% dedicating IT teams to manage cyber risks.
When it comes to cyber crime, the proactive approach to cybersecurity simply means businesses need to be prepared and anticipate a cyber attack. One way of doing this is by adopting a zero trust framework. The zero trust framework addresses the cybersecurity threats of today and design architecture with an assume-breach mindset.
For Duca, a majority of organizations in Southeast Asia have either started or looking to execute a zero trust project. Those that have started it are now looking at how they can implement it properly to get the most out of it.
“I think different organizations are at different levels of maturity as well. The reality is, it’s a changing dynamic environment. Looking at what we’ve experienced of the backdrop of COVID, whereby there were accelerated digital transformation journeys for pretty much every customer, and every organization, the threat landscape, and threat model has changed. We rely on more of a remote and hybrid workforce. And if we start to say, this is the way that we’ve always done it, that will not propel us forward. It will only move us backward. I still think that we’re a lot better than we were. But I think there’s still obviously a lot more room to grow,” commented Duca.
Duca also believes that zero trust is probably the most overly used word in cybersecurity right now. And he explained that this is because everyone has their own different definition.
“The reality and the context around what we believe zero trust is, it’s not just simply a case of getting onto the network and that’s it. It’s not just zero trust network access. For us, it’s all about continuous validation, and inspecting the traffic because people can be in the change overnight. And if we’re not doing that continuous validation, you’ll end up having a scenario where someone simply infiltrate and they were a trusted user,” added Duca.
READ MORE
- Safer Automation: How Sophic and Firmus Succeeded in Malaysia with MDEC’s Support
- Privilege granted, not gained: Intelligent authorization for enhanced infrastructure productivity
- Low-Code produces the Proof-of-Possibilities
- New Wearables Enable Staff to Work Faster and Safer
- Experts weigh in on Oracle’s departure from adland
