
Gantry cranes are seen behind signage for ports operator DP World at an entrance to the Port Botany compound in Sydney on November 13, 2023. Major ports handling nearly 40 percent of Australia’s freight trade may be crippled for days, officials said on November 13, three days after a cyber attack blocked the key gateways. (Photo by DAVID GRAY / AFP)
Why are state-sponsored hackers targeting Australia?
- Australia has been experiencing more and more cyberattacks by state-sponsored hackers.
- The country also reported that 57% of the cybersecurity incidents affected critical infrastructure.
- The DP World cybersecurity incident could also have been a state-sponsored cyberattack.
Australia is witnessing more and more cyberattacks as the government looks to improve the nation’s cybersecurity. The attacks have involved organizations from various industries, with some resulting in heavy financial losses.
In 2022, major cybersecurity incidents involved telcos, healthcare providers, and financial service providers. As a result, the government set up an agency to help coordinate responses to cybersecurity incidents. This also included raising the penalties for companies that did not take cybersecurity seriously, leading to breaches.
According to the Australian Cyber Security Center’s (ACSC) Cyber Threat report developed by the Australian Signals Directorate (ASD), a range of malicious cyber-actors showed the intent and capability needed to compromise vital systems and Australian networks were regularly targeted by both opportunistic and more deliberate malicious cyber-activity.
The report also stated that ASD responded to 1,100 cybersecurity incidents from Australian entities, with nearly 94,000 reports from 2022 to 2023, a 23% increase from the previous year. The average cost of cybercrime also increased by 14%.
“Australia’s region, the Indo-Pacific, is now seeing growing competition on multiple economic, military, strategic, and diplomatic levels, framed by competing values and narratives.
In this context, Australian governments, critical infrastructure, businesses, and households continue to be the target of malicious cyber-actors. This report illustrates that state and non-state actors continue to show the intent and capability to compromise Australia’s networks. It also highlights the added complexity posed by emerging technologies such as AI.
“The report demonstrates the persistent threat that state cyber-capabilities pose to Australia. This threat extends beyond cyber-espionage campaigns to disruptive activities against Australia’s essential services. The report also confirms that the borderless and multi-billion dollar cybercrime industry continues to cause significant harm to Australia, with Australians remaining an attractive target for cybercriminal syndicates worldwide,” said Richard Marles, Australia’s Deputy Prime Minister and Minister of Defense.

State-sponsored hackers are on the rise. (Image generated by AI)
What are state-sponsored hackers?
State-sponsored hackers are cyberattackers who are supported or directed by a government. They may target other countries, organizations, or individuals for various reasons, such as espionage, sabotage, or influence operations.
Some examples of state-sponsored hackers are the APT groups (Advanced Persistent Threats), named by security researchers based on their tactics, techniques, and procedures. Some of the most notorious APT groups are APT28 (also known as Fancy Bear or Sofacy), which is linked to Russia; APT1 (also known as Comment Crew or Unit 61398), which is linked to China; and APT33 (also known as Elfin or Refined Kitten), which is linked to Iran.
State-sponsored hackers pose a serious threat to global cybersecurity and stability, as they can launch sophisticated and stealthy attacks that can cause significant damage or disruption. They can also exploit vulnerabilities in critical infrastructure, such as power grids, water systems, or healthcare facilities. Therefore, it is essential to have effective defenses and countermeasures against state-sponsored hackers.
The rise of state-sponsored hackers
The report showed that Australia has witnessed an increase in state-sponsored hackers recently. Earlier this year, another cybersecurity report by Microsoft also found that Chinese-state-sponsored hackers have been targeting Australia.
Specifically, the state-sponsored hackers are focused on critical infrastructure, data theft, and the disruption of businesses. The report stated that the AUKUS partnership (a partnership between the US, UK, and Australia) is a likely target for these hackers, especially since it focuses on advanced military development and nuclear submarines.
In 2023, ASD joined international partners to call out Russia’s Federal Security Service’s use of ‘Snake’ malware for cyber-espionage and also highlighted activity associated with a China state-sponsored cyber-actor that used ‘living-off-the-land’ techniques to compromise critical infrastructure organizations.
The rise of state-sponsored hackers has also meant that Australia’s critical infrastructure was targeted via increasingly interconnected systems. Given the increasing use of operational technology, cybercriminals are unleashing malicious cyber-actors to attack these systems. In the past year, the ASD has responded to 143 cybersecurity incidents related to critical infrastructure. The vast majority of these incidents were low-level malicious attacks or isolated compromises.
The leading cybersecurity incident types affecting Australian critical infrastructure were:
- compromised account or credentials
- compromised asset, network, or infrastructure
- DOS
The report also highlighted that these incident types accounted for approximately 57% of the critical infrastructure incidents for 2022–23. Other more prominent incident types were data breaches followed by malware infection.
Head of ASD’s ACSC, Abi Bradshaw CSC, shares the release of our 2022-23 #ASDCyberThreatReport. By working together we can stay ahead of cyber threats & make Australia a harder target for malicious cyber actors. Download the report 👉https://t.co/11CRLzyuPf pic.twitter.com/uY8WllvwUW
— Australian Cyber Security Centre (@CyberGovAU) November 15, 2023
Was Australia’s major port operators hack a state-sponsored attack?
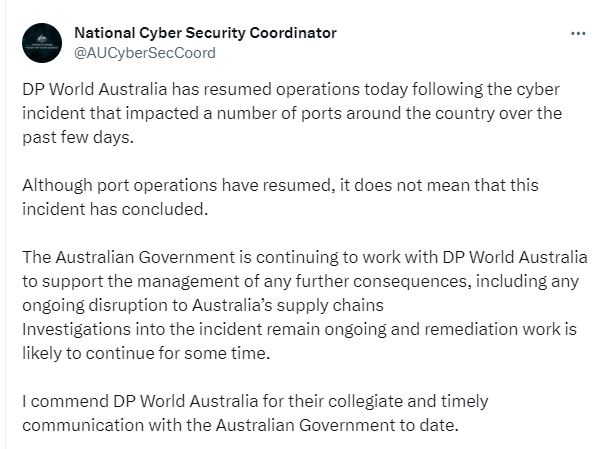
Given the details in the report, could the recent cyberattack on operations at DP World Australia be a state-sponsored attack? While reports show that the port is back online after being crippled by cybercriminals, investigations have yet to confirm who exactly perpetrated the cyberattack.
The incident disrupted operations in port terminals in Melbourne, Sydney, Brisbane, and Perth from the 10th-13th of November. The firm manages around 40% of the goods entering and leaving the country.
According to a report by the BBC, Darren Goldie, the Government’s cybersecurity coordinator, said the operator was making “good progress” at bringing its sites back online. DP World Australia, a unit of the Dubai state-owned DP World, said its ports resumed operations at 09:00 local time “following successful tests of key systems overnight.”
The company also explained that it halted internet connectivity at its ports to prevent any ongoing unauthorized access to its network. The Australian government continues to work with DP World Australia to support the management of any further consequences, including any significant disruption to Australia’s supply chains. Investigations into the incident are ongoing, and remediation work will likely continue for some time.
As yet, it’s unknown whether the DP World cyberattack was the work of state-sponsored hackers, but the importance of the organization means it can’t yet be ruled out.
However, that was not the only thing causing problems at the ports of Australia.
Over the weekend, there had been increased Pro-Palestinian protests in the country, with reports claiming that some protestors had intended to block shipments from leaving Australia.
A report by Al-Jazeera stated that the protests at Sydney’s Port Botany, followed by similar protests at the Port of Melbourne, saw activists lie down in front of trucks carrying cargo for the Israeli shipping company Zim. Some activists allegedly even resorted to riding jet skis to stop the ship from leaving the port.
It remains to be seen if the protests are linked to the ports being targeted by cybercriminals. However, there have been increasing numbers of cyberattacks on countries that have been supporting either Israel or Palestine since the conflict began a month ago.
READ MORE
- Safer Automation: How Sophic and Firmus Succeeded in Malaysia with MDEC’s Support
- Privilege granted, not gained: Intelligent authorization for enhanced infrastructure productivity
- Low-Code produces the Proof-of-Possibilities
- New Wearables Enable Staff to Work Faster and Safer
- Experts weigh in on Oracle’s departure from adland





