
Why a secure SDLC process is important for the finance industry
FINANCIAL services companies know that gaining a competitive edge in the digital era is about optimizing the “time-to-market” of new solutions and offerings.
Companies that beat their rivals in rolling out a new app or improved features will maintain the upper hand in the market.
To achieve this, organizations everywhere have adopted DevOps and Agile methodologies to ensure rapid delivery of new apps and solutions, and their upgrades.
While the speedy development process is working like a charm, it poses a whole new set of challenges for security teams.
The truth is, cyberthreats have inherently become more complex in recent times, and application security risks have become multi-dimensional.
In the days of monolithic applications and closed network, it might have been alright to leave security at the tail end of the process, but the age of digital transformation requires a different, security-first approach.
This is especially true in the banking and the financial services industry which is constantly defending itself from cybercriminals and bad actors.
Nearly all banks and fintech firms now feature an online portal as well as mobile apps as a result of consumer demand — and there’s increased pressure to continually upgrade digital offerings.

This is exactly why the industry is constantly on the lookout for new and interesting ways to improve how it defends against cyber threats. The first step, of course, is to secure the code in their applications.
Establishing a secure SDLC process
Although banks and financial institutions are constantly under attack in cyberspace, not all of the attack vectors used to target them are sophisticated.
Many simple and complicated attacks can be prevented if the team uses iterative DevOps delivery and faster release cycles, ensuring that security is foundational and built into the software development life cycle (SDLC).
To that end, organizations must first establish security requirements for the apps that they are building. Development and security teams should also identify and figure out the critical risks of the app and if there are any industry or regulatory standards that they need to adhere to.
A clear line of communication has to be established between the development team and the security team, and development should only begin once proper security standards are set.
In addition to that, organizations should also run a thorough analysis of the attack surface or the various areas of risk potentially posed by the app.
These attack surfaces are generally the paths and commands of the app, critical data used in the app, and most importantly, codes that protect these paths and data.

Source: Checkmarx
Perhaps the most critical step of instilling security into the SDLC process is to perform static analysis security testing or SAST.
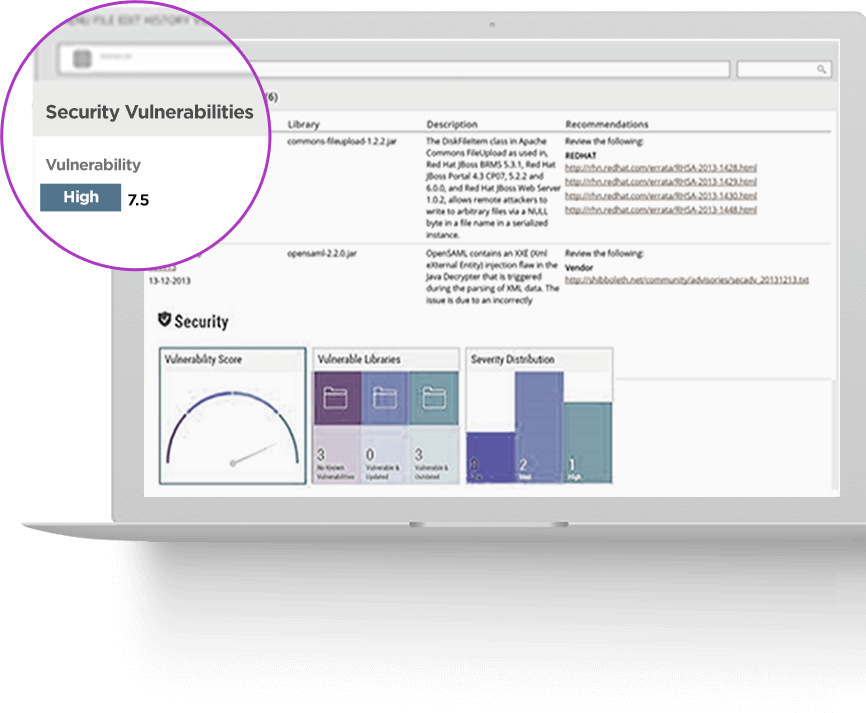
SAST basically scans the source code of an application to detect critical vulnerabilities, and some advanced versions of the tool can run automatically, even on codes that are yet to be compiled.
By performing SAST, development teams can identify and subsequently secure the code from the very beginning, laying a strong and secure foundation at the early stages of the development.
Further, SAST also scans for issues pertaining to compliance and industry standards, such PCI-DSS, which many financial institutions are subjected to.
Following SAST, development teams should also test the live version of the app using interactive application security testing (IAST).
IAST tools are generally designed to work in DevOps environments, where it looks for vulnerabilities on a running application by leveraging existing functional testing activities, without affecting the SDLC process.
While establishing a secure SDLC may have been a significant challenge in the past, organizations could easily rely on vendors that offer fully integrated platforms to help achieve their security goals.
Source: Checkmarx
Picking the right app security platform could be understandably daunting for any business leader. Tech Wire Asia combed through a list of leading app security providers in the market, and found one that it could recommend.
Checkmarx: A single platform for all your security needs
When it comes to finding a one-stop, unified, enterprise-grade platform with all the right features, nothing comes close to Checkmarx’s Software Security Platform.
The platform’s holistic approach perfectly aligns security into DevOps methodologies and embeds security into every step of the SDLC.
At the heart of the platform is Checkmarx’s industry-leading source code analysis solution, CxSAST, a highly accurate and flexible tool which enables development teams to automatically scan codes – including those that are uncompiled – to seek out security vulnerabilities.
The ability to scan raw source code essentially allows companies to integrate security at the earliest stage of the development lifecycle.
Beyond that, Checkmarx also optimizes remediation efforts with its unique “Best Fix Location”, which identifies critical points in code segments that neutralize multiple security vulnerabilities with a single fix.
Meanwhile, Checkmarx’s Interactive Application Security Testing (CxIAST) detects vulnerabilities in applications under test integrating seamlessly into any organization’s CI/CD pipeline, providing advanced vulnerability coverage and more intelligent remediation without any impact on testing cycle times.
With CxSAST, CxIAST, and CxOSA that detects open source components and associated risk factors, Checkmarx’s Software Security Platform is the ideal platform for DevOps success.
Click here to read more about Checkmarx’s Software Security Platform.
*Some of the companies featured are commercial partners of Tech Wire Asia
READ MORE
- Strategies for Democratizing GenAI
- The criticality of endpoint management in cybersecurity and operations
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
