
Making behavioural analytics a cybersecurity defensive force with ExtraHop

Attend any cybersecurity conference or exhibition anywhere in the world, and despite the presence of multiple vendors attempting to sell their wares, you simply won’t hear from any company the claim that its solution is the be-all and end-all of cybersecurity. There is no such thing as an all-powerful, all-pervasive solution to the dangers of a cyber incursion and data exfiltration or compromise.
That’s not to say, of course, that every cybersecurity measure is equally compelling. Most enterprise security teams adopt multiple complementary solutions, the combination of which is as effective as possible at any given moment.
Just as even the most sea-worthy of vessels keep pumps close to the keel, however, even the most robust of cybersecurity infrastructures must be prepared for attackers to find a way in.
If we accept that cybersecurity defences will be breached at some point (or more likely, several times), and that modern business runs on-premises —where BYOD policies can mean endpoint numbers change by the second— as well as in the public and private cloud, how can companies survive?
The answer is that many organisations are taking their defences up a notch or two by deploying one of the first practical and real-world uses of machine learning and, to a developing degree, artificial intelligence in the workplace. True, amid the claims of every new product under the sun being “powered by AI,” it’s easy to be sceptical. But in cybersecurity settings, ML and emerging systems of AI are very well suited to helping protect enterprise networks.
The perfect fit for behavioural analytics
If we consider that behavioural analytics like machine learning and AI are different from static computer code in that these services improve their own performance over time, we must think about how those improvements are made. Invariably, the process of improvement takes place as the systems learn patterns and apply knowledge of common behaviours to any situation going forward. Consider image recognition: show a computer enough pictures of cats and, sooner or later, the silicon brain may not recognise a dog but will be able to raise a flag against the presence of a “non-cat.”
The more cat pictures the computer brain is given, the more accurate the sniffing out of interlopers among the feline hoards.
In cybersecurity, instead of image patterns, ML systems learn patterns of data behaviour from very large data sets — the bigger, the better. The Accounts Director’s laptop, for instance, accesses a finite number of internal and cloud-based systems, day in and day out. Each access is categorised by a pattern — the typical size of data interchange, method of logging in, average time of operation, and so on.
If the Accounts Director’s laptop is compromised after a rogue email is clicked, and a small malware installs, any subsequent behaviour that deviates from the expected patterns will raise a red flag.
The ability to detect subtle attack behaviours that might not match a known malware signature is particularly effective given the intelligent nature of the modern hacker. Anti-malware may find evidence of a virus or incursion and delete a rogue .exe, for instance, but three months later, the malware’s hidden payload may start to probe the network to discover domain services. Endpoint scans would come up clean in that scenario, but ML monitors would notice a quiet, malicious network scan taking place long after an incident that’s been “cleaned up.” Odd behaviour is, after all, odd behaviour.
The perfect type of ML
Network traffic analysis that examines each node’s activities (and learns each node’s roles in the network’s overall collection of process) has been found to detect threats 95 percent faster than “traditional” methods of cybersecurity, according to metrics reported by ExtraHop, with particular regard to that company’s Reveal(x) network detection and response (NDR) solution.
As you might expect, turning a machine learning engine into a cybersecurity powerhouse isn’t necessarily a case of plugging in a couple of cables, or implementing a cloud-based ML service like that offered by ExtraHop Reveal(x) and calling it a day. ML should complement and empower the human analysts ready to respond to complex threats.
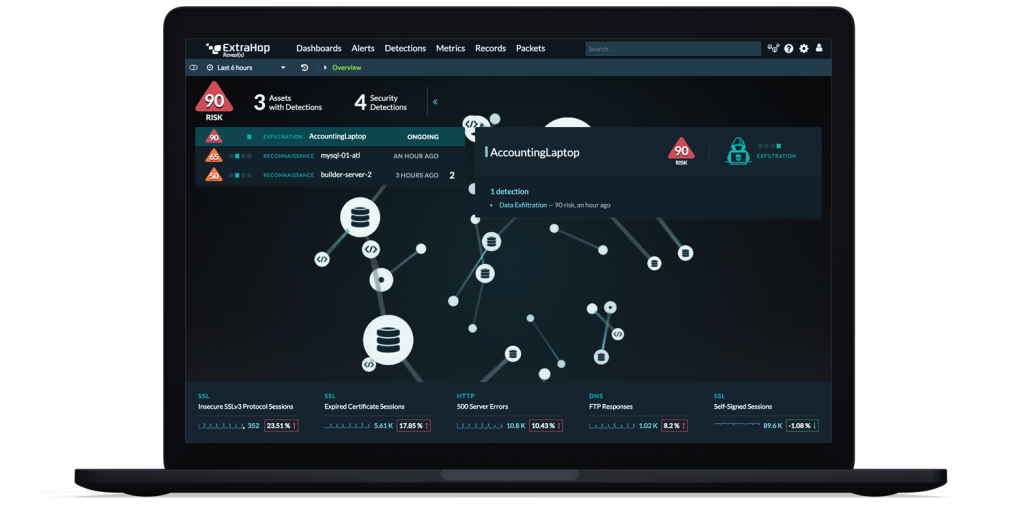
Source: ExtraHop
With that said, any degree of effective ML or AI-based system is an improvement on a “traditional” IF <pattern x> OR <pattern Y> OR <pattern z>>THEN… approach. Blacklisting or whitelisting in a binary manner is still a useful model of threat detection, but only for cybersecurity’s easier targets.
Bespoke cybersecurity-specific ML engines that create an intelligent zero-trust framework are currently the best solution available to companies hoping to (better) protect their networks. But ExtraHop, for example, is very clear that its solutions should form a part of — and only a part of — an overall cybersecurity provision. Reveal(x) fits in neatly with more “traditional” cybersecurity and network operations practices and solutions as a network detection and response tool designed to complement endpoint detection, response and SIEM (logging/security information and event management). Because Reveal(x) is dedicated to NDR, there are specific use-cases it can meet that other tools cannot.
Take the example of encrypted traffic. The Reveal(x) platform can request encryption keys to decrypt, examine, and re-encrypt east-west traffic. That sort of specialist application could be achieved by two or three proprietary applications strung together and a likely negative impact on performance, but that capability comes built into the ExtraHop stack and operates entirely out-of-band.
Throw into the mix that the platform also provides deep context and recommended steps for further investigation, and third-party integration for automated incident response, and the advantages of a dedicated solution by a dedicated provider become clear.
Real-time threat detection and response from ExtraHop is not the golden bullet that will kill the bad actor’s every weapon and method, but it plays a pivotal role in mitigating the damage that might result from the inevitable incursions that every enterprise will suffer.
There’s no substitute for human judgement and skills in cybersecurity technology, but a machine learning-based set of protective software applications is significantly more effective than cyber protection methods from only a couple of years ago. Find out how your enterprise can be better protected by speaking to an ExtraHop representative today.
READ MORE
- Strategies for Democratizing GenAI
- The criticality of endpoint management in cybersecurity and operations
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
