
Zero-trust security in the age of infrastructure as a service (IaaS)

When BYOD became a reality for businesses across the globe (around the time of the launch of the original iPhone back in 2007), the IT security industry had to learn to cope with protecting the business from a new generation of threats, carried into networks by employees every day.
Later, as cloud services became more common, the same professionals had to cope with shadow IT — when individuals, workgroups and teams of developers started to spin up new instances of online apps and services, often without the specific approval of the IT department.
IT security’s role changed accordingly; to protect users and data wherever they might exist— on portable devices, in multiple cloud services, on-premise, or in local data centers.
In 2020, entire infrastructures are now available as services, with all elements of enterprise IT either real or abstracted in multiple cloud providers’ data centers. Most enterprises now use a mixed (or hybrid) topology, spreading software development functions, testing, and live production services across AWS, Google Cloud, Alibaba, on-premise, and even at remote edge installation sites.
What’s often not realized is that the ease of use and power of IaaS (infrastructure as a service), commonly available for prices as low as a few cents an hour, obscures the inherent security issues that misconfiguration and misuse of those systems can produce. And although the assumption might be widely held that the cloud providers’ security systems are first-rate and effectively bullet-proof, it’s the enterprise using the cloud provision that’s entirely responsible for its own data safety and governance.
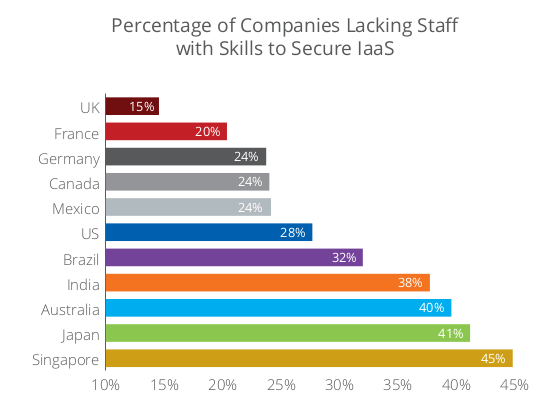
As a survey (PDF) of over 1,000 enterprises across 11 countries shows, millions of customer records and valuable intellectual property of all types are in significant danger of attack — and all without the need of hackers to deploy a single line of malware code.
Mis-steps & misconceptions
As is often the case in IT security issues, perceptions of threats usually underestimate the realities. Unfortunately, mismatches exist in the field of IaaS security provisions, both in terms of what’s occurring every month for most enterprises, but also between C-Suite executives and their CISO- and CTO-level managers.
Even the starting metrics are incorrect in a business’s evaluations, the survey found. Seventy-six percent of the over 1,000 responding companies thought they used multiple IaaS suppliers, but the reality was that 92 percent actually do— a rise of 18 percent, year on year.
And when quizzed as to how many incidents took place each month as a result of IaaS misconfiguration, the answer averaged 37. However, on closer examination by an independent third-party, the figure was found to be 3,500 incidents per month. That means that over 99 percent of potential data breaches resulting from IaaS misconfigurations are going unnoticed!
The anatomy of an attack
A cloud-native data breach takes a different shape from what might be regarded as “normal” by bad actors.
A typical CNB comprises three steps:
Land. The attacker gains a foothold into a single IaaS setting, typically using compromised credentials, the exploitation of a vulnerability like a server-side request forgery (SSRF), or a misconfigured security group structure.
Expand. From the initial node, an attacker can move “sideways” using knowledge gained by simple probing of other connected apps and services in the VPC (virtual private cloud).
Exfiltrate. Once valuable data is identified, it can be removed, often by encrypted egress or via a Tor connection that terminates elsewhere.
Exacerbation by automation and more
In development environments, the need for speed and efficiency has led to a high degree of automation in continuous dev & integration processes.
Unfortunately, while these highly efficient processes reduce time-to-production figures, any misconfiguration is also replicated and distributed.
While the survey states that 78 percent of misconfigurations are corrected in IaaS topologies within hours or minutes, that leaves 22 percent of errors present for days (20 percent) or months (two percent).
Note that those figures are averages, as there’s a good deal of variation in the security performance of teams in divergent geographies. In Singapore and Japan, for instance, not only are responses to misconfigurations quicker, but those countries are also better equipped with trained staff than their UK or US-based colleagues.
Be that as it may be, development activities that mirror “shadow IT”— that is, teams creating workloads and accounts outside of those defined by management— pose the significant risks.
Clearly, when containerization and automated virtualized resource deployments are factored in, the security posture of the enterprise can be compromised quite significantly. That’s because of several factors that especially define containers and technology like Kubernetes.
Containers and virtualization
The potential ephemeral nature of containers in production environments (a single instance may only “live” for a few seconds) makes security audits in the traditional sense relatively pointless.
Even a full virtual machine created in an IaaS for purposes of testing may only last for a few hours but could easily have unhindered access to the rest of the cloud’s apps and services.
Misconfigurations are therefore difficult to spot, and once replicated, almost impossible to trace in every instance across the entire virtual WAN.
Preventing data loss
Companies are now deploying DLP (data loss prevention) platforms specifically in cloud settings to stop data leaving the enterprise.
These solutions are, however, more typically used to prevent employees and ex-employees from taking data manually from the business, whether by accident or malicious design. But the survey notes that such platforms have tracked 248 percent more DLP incidents in 2019 (5,314 incidents) than in 2018 (1,527) on average.
Solutions and tools
Activities that take place in virtual environments like IaaS clouds are challenging to track, but there are platforms and tools on the market that can help security teams.
DLP platforms have already been mentioned, but there are also various options for UEBA (User and Entity Behavior Analytics) trackers that can show the prevalence of lateral movements across complex hybrid networks that may indicate the “expand” stage of a possible incident.
As is often the case, there’s a degree of user education that’s necessary, in addition to the use of physical code layers that help protect. In the case of development teams, this may come more quickly than in other areas of the enterprise; DevOps professionals will have an immediate grasp of the issues without needing the issues “translating” into simpler terms.
Nevertheless, integrating safer practices into workflows and automation systems in the enterprise will take time, and require a significant change in mindset: zero-trust and security-first are now concepts that every part of the enterprise needs to embrace.
For more information about the preventative measures open to security teams of any size, shape, and hue, we recommend you speak to an expert in the relevant issues at McAfee today.
READ MORE
- Strategies for Democratizing GenAI
- The criticality of endpoint management in cybersecurity and operations
- Ethical AI: The renewed importance of safeguarding data and customer privacy in Generative AI applications
- How Japan balances AI-driven opportunities with cybersecurity needs
- Deploying SASE: Benchmarking your approach
