Source: Shutterstock
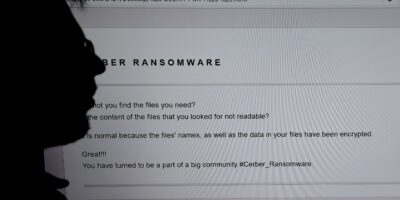
Should we be insuring against ransomware?
- The threat of ransomware is rising rapidly. Successful attacks can be devastating to businesses, who frequently pay up to recover systems and data
- Insurance providers are now offering cover to reimburse the cost of ransom payments
- But cybersecurity commentators have accused the practice of conflagrating the ransomware issue and “funding organized crime”
The insurance industry is built on covering financial risks to individuals and businesses so that an insurance market has emerged to cater to the potential damage inflicted by ransomware demonstrates just how common the cybersecurity threat has become.
Indeed, in Q3 2020, Check Point Research saw a 50% increase in the daily average of ransomware attacks, compared to the first half of the year. This was led by two ‘strains’, Maze and Ryuk, the latter of which now attacks 20 organizations a week.
Given this surging threat – exacerbated by a more digital reliance than ever among businesses and evermore sophisticated phishing techniques and malware – businesses are turning to insurers to cover themselves against the potentially crippling ransoms accompanying successful threats – which can be in the tens of millions of dollars.
One of the most high-profile and successful attacks in 2020 saw GPS technology and fitness firm Garmin eventually pay an estimated US$10 million to recover systems and data.
It’s not just private companies that are being targeted. Often cybercriminals choose their targets based on causing maximum disruption to society. Public service organizations, universities, and hospitals are frequent victims.
Germans police launched a homicide investigation in September after a woman died during a cyberattack on a hospital in Dusseldorf, as doctors attempted to transfer the patient to another facility.
Paying ransoms, whether directly or by proxy via an insurance firm, is a controversial practice. Many in the cybersecurity field believe that by paying out claims from companies who have paid ransoms to regain access to data and systems after an attack, insurers are inadvertently supporting organized crime, and contributing to ransomware’s growth.
Ciaran Martin was the head of the UK’s National Cyber Security Centre until last August, and said ransomware was “close to getting out of control”, fuelled by the fact there is no legal barrier to companies paying ransoms to cybercriminal gangs, and claim their loss back on insurance.
Extortion laws prohibit the payment of ransoms to terrorists, in response to the threat of kidnapping. However, cyberattacks aren’t carried out by terror groups (not knowingly, at least). The most prolific tend to be based in Russia or former Soviet states, operating while the Kremlin and other governments turn a blind eye.
As such, there’s no bar to paying ransom demands, so it’s possible to make a claim if no personal data is involved.
“I see this as so avoidable. At the moment, companies have incentives to pay ransoms to make sure this all goes away,” the former intelligence chief said. “You have to look seriously about changing the law on insurance and banning these payments, or at the very least, having a major consultation with the industry.”
Following Martin’s comments and accused of funding organized crime, the UK insurance industry has hit back.
As reported by the BBC, The Association of British Insurers (ABI) has defended the inclusion of ransomware payments in first-party cyber-insurance policies, stating that insurance was “not an alternative” to doing everything possible to minimize the risk.
Paying ransom demands can be incredibly tempting to organizations, offering them a way to admit a loss, sweep the problem away under the rug, and get business back and running as quickly as possible. Taking a stand against it is much harder.
Aluminum firm Norsk Hydro was attacked in 2019, causing the shutdown of its entire IT system – 22,000 computers were hit at 170 sites across 40 countries worldwide.
Despite being insured against cyberattacks, the firm refused to pay, instead of shifting to manual operations in order to keep the business operational at barebones capacity.
Recovery cost the business an estimated US$45 million, and profits dropped by 82% in the immediate aftermath. Nonetheless, the company was praised for its response.
Just like houses require security systems and cars require inspections, insurers do require that reasonable precautions are taken to prevent cyberattacks from succeeding, and these requirements could ultimately contribute to cybersecurity across businesses.
On the flip side, insurance could lull businesses into a false sense of security which attackers could take advantage of.
“Cyber is a relatively immature insurance market without historical loss data to guide it. The rapid increase in the number and value of attacks may show insurers that continuing this cycle will make it unprofitable,” said Peter Groucutt, Managing Director at Databarracks.
Groucutt believes insurers should focus on two key areas when approaching the ransomware issue.
“Firstly, as with other types of cover, insurance companies must carry out cyber hygiene checks on customers before entering an agreement. For smaller organizations that could mean having the Cyber Essentials Certification, or for larger organizations, a more thorough assessment of its cyber defenses and backup and recovery provisions.
“Secondly, insurers should rework their approach when an incident does happen. Rather than paying out to cover the cost of a ransom, they should emphasize remediation, so fixing the problem by helping the customer with Cyber Incident Response, IT Forensic Services and assistance to restore data and get operations back up and running.”
Groucutt concluded: “This change won’t happen overnight: it will be a case of short-term pain but long-term gain. Whether done proactively or through regulation it will take time and effort, but this zero-tolerance approach is our best chance at breaking the cycle. This is in insurers’ and their customers’ best interests in the long run.”
READ MORE
- Safer Automation: How Sophic and Firmus Succeeded in Malaysia with MDEC’s Support
- Privilege granted, not gained: Intelligent authorization for enhanced infrastructure productivity
- Low-Code produces the Proof-of-Possibilities
- New Wearables Enable Staff to Work Faster and Safer
- Experts weigh in on Oracle’s departure from adland