
The education sector is highly targeted by cybercriminals. (Image – Shutterstock)
Why ransomware protection is essential for the education sector
|
Getting your Trinity Audio player ready... |
- The education sector reported the highest number of ransomware attacks in 2022.
- The education sector also has one of the highest rates of ransom payment.
- Exploits and compromised credentials accounted for more than 77% of ransomware attacks.
Ransomware protection should be a prerogative for organizations today, especially with the increasing number of cyberattacks taking place. While most organizations have implemented a variety of cybersecurity measures to deal with threats, cybercriminals are still finding ways to get past them and wreaking havoc on businesses.
Today, cybercriminals are going after every business in every industry. Be it the financial or manufacturing sector, the healthcare or the oil and gas industry, these companies continue to be continuously targeted. In fact, Sophos’ State of Cybersecurity 2023 report highlights that with 94% of organizations experiencing a cyberattack of some form in the last year, all companies – regardless of size or revenue – should assume they will be a target in 2023. As such, organizations in these industries continue to invest heavily in ransomware protection to improve their cybersecurity.
Interestingly, according to a report by Sophos, the education sector reported the highest number of ransomware attacks in 2022. The State of Ransomware in Education 2023 found that over the past year, 79% of higher educational organizations surveyed reported being hit by ransomware, while 80% of lower educational organizations surveyed were targeted—an increase from 64% and 56% in 2021, respectively.
The education sector has long been a goldmine for cybercriminals. Not only are education institutions lacking ransomware protection, but the amount of data available is also heavily in demand on the dark web. This is why the sector reported one of the highest rates of ransom payment with more than half (56%) of higher educational organizations paying and nearly half (47%) of lower educational organizations paying the ransom.
But there is a problem with this. When organizations pay the ransom, it also significantly increases recovery costs for both higher and lower educational organizations. Recovery costs (excluding any ransoms paid) for higher educational organizations that paid the ransom were US$1.31 million when paying the ransom versus US$980,000 when using backups. For lower educational organizations, the average recovery costs were US$2.18 million when paying the ransom versus US$1.37 million when not paying.
Is the education sector doing enough to deal with ransomware?
An easy target for cybercriminals
Paying the ransom also lengthened recovery times for victims. For higher educational organizations, 79% of those that used backups recovered within a month, while only 63% of those that paid the ransom recovered within the same timeframe. For lower educational organizations, 63% of those that used backups recovered within a month versus just 59% of those that paid the ransom.
“While most schools are not cash-rich, they are very highly visible targets with immediate widespread impact in their communities. The pressure to keep the doors open and respond to calls from parents to ‘do something’ likely leads to pressure to solve the problem as quickly as possible without regard for cost. Unfortunately, the data doesn’t support that paying ransoms resolves these attacks more quickly, but it is likely a factor in victim selection for the criminals,” said Chester Wisniewski, field CTO, of Sophos.
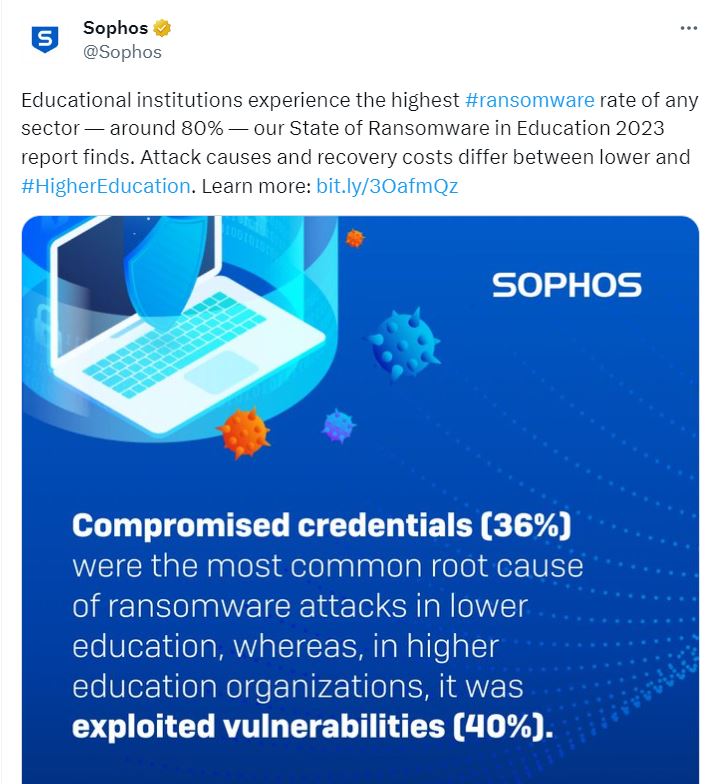
The report also stated that the root causes of ransomware attacks in the education sector were similar to those across all sectors. However, there was a significantly greater number of ransomware attacks involving compromised credentials for both higher and lower educational organizations (37% and 36% respectively versus 29% for the cross-sector average).
Additional key findings from the report include:
- Exploits and compromised credentials accounted for more than three-fourths (77%) of ransomware attacks against higher educational organizations; these root causes accounted for more than two-thirds (65%) of attacks against lower educational organizations.
- The rate of encryption stayed about the same for higher educational organizations (74% in 2021 versus 73% in 2022) but increased from 72% to 81% across lower educational organizations during the past year.
- Higher educational organizations reported a lower rate of using backups than the cross-sector average (63% versus 70%). This is the third lowest rate of backup use across all sectors. Lower educational organizations, on the other hand, had a slightly higher rate of using backups than the global average (73%).
“Abuse of stolen credentials is common across sectors for ransomware criminals, but the lack of adoption of multifactor authentication (MFA) technology in the education sector makes them even more at risk of this method of compromise. Like the U.S. federal government’s initiative to mandate all agencies use MFA, it is time for schools of all sizes to employ MFA for faculty, staff and students. It sets a good example and is a simple way to avoid many of these attacks from getting in the door,” added Wisniewski.
The need for ransomware protection
As universities, colleges, schools and other learning institutes continue to be targeted, having adequate ransomware protection is key. Apart from backup and recovery capabilities, Sophos also recommends the education sector strengthen its defensive shield with security tools that defend against the most common attack vectors. This includes endpoint protection with strong anti-exploit capabilities to prevent exploitation of vulnerabilities, and Zero Trust Network Access (ZTNA) to thwart the abuse of compromised credentials.
The education sector should also consider investing in adaptive technologies that respond automatically to attacks, disrupting adversaries and buying defenders time to respond. There should also be considerations for 24/7 threat detection, investigation and response, whether delivered in-house or by a specialist Managed Detection and Response (MDR) provider.
Apart from that, ransomware protection can also be achieved through optimizing attack preparation, including making regular backups, practicing recovering data from backups and maintaining an up-to-date incident response plan. Learning institutes should also maintain good security hygiene, including timely patching and regularly reviewing security tool configurations.
The State of Ransomware 2023 survey polled 3,000 IT/cybersecurity leaders in organizations with between 100 and 5,000 employees, including 400 from the education sector, across 14 countries in the Americas, EMEA and Asia Pacific. This includes 200 from lower education (up to 18 years) and 200 from higher education (above 18 years) and both public and private sector education providers.
READ MORE
- Safer Automation: How Sophic and Firmus Succeeded in Malaysia with MDEC’s Support
- Privilege granted, not gained: Intelligent authorization for enhanced infrastructure productivity
- Low-Code produces the Proof-of-Possibilities
- New Wearables Enable Staff to Work Faster and Safer
- Experts weigh in on Oracle’s departure from adland


